After my TestTalks interview with Troy Hunt a few years ago I was shocked just how easy it was for someone to hack my APIs using some common Api Security Test Tools. Are you aware that anyone can easily see your API traffic? With the Internet of Things (IoT) era now upon us—as well as the rise of microservices—more and more modern development is being based on application programming interfaces (API). With this change comes new security concerns and attacks that we’ve not previously seen and need to prepare for.
Listen to my full interview with Troy Hunt:
(FYI: I originally wrote this article for TechBeacon)

Hacked API Example
This past January, we saw an example of an API insecurity when a flaw in Nest thermostats was revealed. The flaw caused users’ location information to be exposed over the Internet. The main cause of the breach? Sensitive user data was being passed over the network in clear text. Anyone with the ability to view the network traffic could have easily gotten the unencrypted Nest communication.
You might say, “So what? Isn’t it hard to get at this information?” But it’s much easier to expose these types of API securities flaws than you think. Using open source tools such as Fiddler, Wireshark, and Metasploit can quickly reveal your application’s network traffic, as well as how hackers can exploit your API and application vulnerabilities.
OWASP
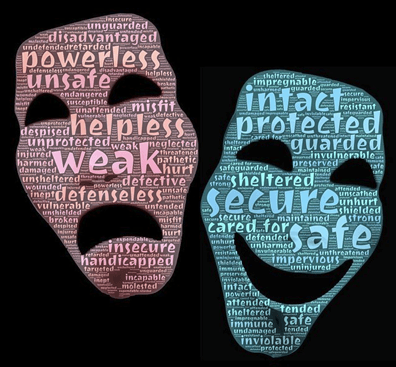
Because API communication occurs under the covers and is unseen, some developers get a false sense of security, believing that no one is really going to poke around to find their API’s vulnerabilities. In my experience, however, HTTP/HTTPS-based APIs can be easily observed, intercepted, and manipulated using common open-source tools.
But before we even start to look at the tools that can help with API security, the first thing to do is identify the current risks in your applications. A great free resource to help you get started is the Open Web Application Security Project (OWASP). OWASP is a well-known, not-for-profit organization that produces a number of different artifacts about web security. One of those artifacts is called the OWASP Top 10 Web Application Security Risks, which, although not specific to APIs, can give you some ideas on where to get started.
Remember, most attacks that are possible on any web application are possible against an API as well. OWASP has a handy Risk Rating Methodology to help you measure your risk. Basically, it can be can be broken down into a simple formula: risk = likelihood of attack, multiplied by what the impact would mean to your application and your business if that risk was exploited.
3 FREE tools for securing your API
Once you know which areas of your APIs are most open to risk, you can begin focusing your efforts on utilizing some tools to start testing and shoring up your vulnerabilities against possible attacks.
Fiddler
Fiddler is a free open source tool that allows you to monitor, manipulate, and reuse HTTP requests. Fiddler does many things that allow you to debug website issues, and with one of its many extensions, you can accomplish even more.
Some things you might want to use Fiddler for:
- Troubleshooting issues with your web application
- Security testing
- Performance evaluations
- Debugging web traffic from most computers and devices
Fiddler is already a pretty popular tool among many developers. Many use it for debugging to look at the HTTP request their PC is sending to a service or website. What a lot of engineers don’t know, however, is that Fiddler can actually act as an HTTP proxy.
Listen to my interview with the creator of Fiddler Eric Lawrence:
When you go into the settings in Fiddler, there’s a Connections tab that allows you to select a Remote Connections setting. Once you’ve ticked that setting, you can go to your iPad or any other device that you can configure a proxy on and tell it to use the IP address of your PC as a proxy.
Effectively, what will then happen is that everything you do on that device will be routed through Fiddler. Just as you can open Fiddler and see all the requests from your PC, you can also see all the requests from this external device. That’s how simple it is to actually see how a device is communicating with its back end. Using this setting will allow you to scan the traffic going on between your device and server, and scan for the same clear-text issue that was exposed on the Nest thermostat.
As a matter of fact, there is a training course by Troy Hunt called Hack Yourself First, and Fiddler is the only tool he uses to exploit all kinds of security issues.
Although Fiddler is probably the easiest tool to begin testing your APIs, another common tool you can use is Wireshark.
Wireshark
Wireshark is a protocol analysis tool, and it’s also a great way to bridge the gap between your network, developers, and testers. Whereas Fiddler is geared much more toward HTTP-type debugging, Wireshark can do all of that and more. With Wireshark, you’re really getting down beneath just the HTTP level, which is where Fiddler tends to live, to individual packets across all sorts of different protocols.
Wireshark not only allows you to see your HTTP requests, but it can actually analyze that information. Its main focus is debugging network issues, which is good because the network is probably one of the most overlooked areas of software development. Using Wireshark can help you quickly uncover issues in your application that you may not even be aware of early on in the development process.
Security-wise, it allows you to set a network interface into a promiscuous mode to be able to view all of its traffic. You can then monitor your network traffic and probe network packets that may contain sensitive data that hasn’t been encrypted.
Metasploit Framework
While Fiddler and Wireshark were developed mainly to help developers and network engineers troubleshoot issues, Metasploit Framework was designed specifically for penetration testing—like how to attack MS SQL, browser-based and file exploits, and social engineering attacks. This is one of the main tools used by hard-core security professionals.
Metasploit contains a suite of tools that can help you do things like perform attacks and test security vulnerabilities. It contains a number of different modules that can test your application against common vulnerabilities that many hackers exploit. You can also use it to develop your own exploits. In Metasploit, a module is a software component that performs a chosen attack on a specified target.
With Metasploit, you run commands that choose a module that contains an exploit that you want to run against your application in order to try to break it. For example, many REST API’s rely heavily on SSL. Using Metasploit, you can test your system to see how it handles common SSL exploits like the infamous Heartbleed vulnerability. Metasploit has hundreds of exploits you can use and, of the three tools we’ve covered, is the most complicated. But it also offers the most penetration testing-specific features.
Avoid API Hacks
Remember, as the saying goes, with great knowledge comes great responsibility. The goal of this article is to alert you to the dangers of not thinking about security as you are developing your APIs. Just because your API doesn’t have a user interface doesn’t mean that it is any less susceptible to hacking.
Fiddler, Wireshark, and Metasploit are just a few of the many tools you can use to test your applications and your APIs’ security before a hacker does.

Joe Colantonio is the founder of TestGuild, an industry-leading platform for automation testing and software testing tools. With over 25 years of hands-on experience, he has worked with top enterprise companies, helped develop early test automation tools and frameworks, and runs the largest online automation testing conference, Automation Guild.
Joe is also the author of Automation Awesomeness: 260 Actionable Affirmations To Improve Your QA & Automation Testing Skills and the host of the TestGuild podcast, which he has released weekly since 2014, making it the longest-running podcast dedicated to automation testing. Over the years, he has interviewed top thought leaders in DevOps, AI-driven test automation, and software quality, shaping the conversation in the industry.
With a reach of over 400,000 across his YouTube channel, LinkedIn, email list, and other social channels, Joe’s insights impact thousands of testers and engineers worldwide.
He has worked with some of the top companies in software testing and automation, including Tricentis, Keysight, Applitools, and BrowserStack, as sponsors and partners, helping them connect with the right audience in the automation testing space.
Follow him on LinkedIn or check out more at TestGuild.com.
Related Posts
After blogging about testing for over fifteen years, I realized something embarrassing a while back: I’d never actually sat down […]
Bottom Line: Kobiton is the first real device testing platform I’ve seen that makes AI-powered mobile testing feel like it […]
Look, most of the AI testing tools I cover on the TestGuild Automation Podcast share two things in common: they’re […]
At least one in five people has some kind of impairment, so it’s important to have them in mind when […]